A security analyst sees some suspicious entries in a log file from a web server website, which has a form that allows customers to leave feedback on the company’s products. The analyst believes a malicious actor is scanning the web form. To know which security controls to put in place, the analyst first needs to
determine the type of activity occurring to design a control. Given the log below:
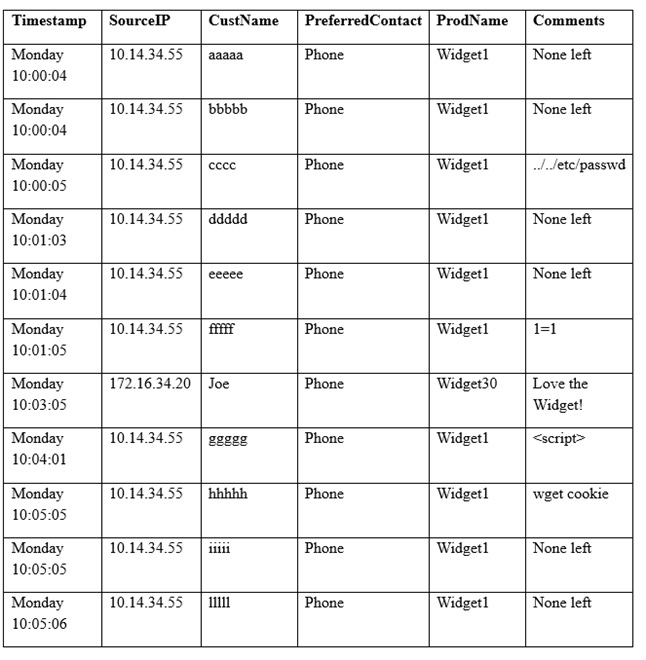
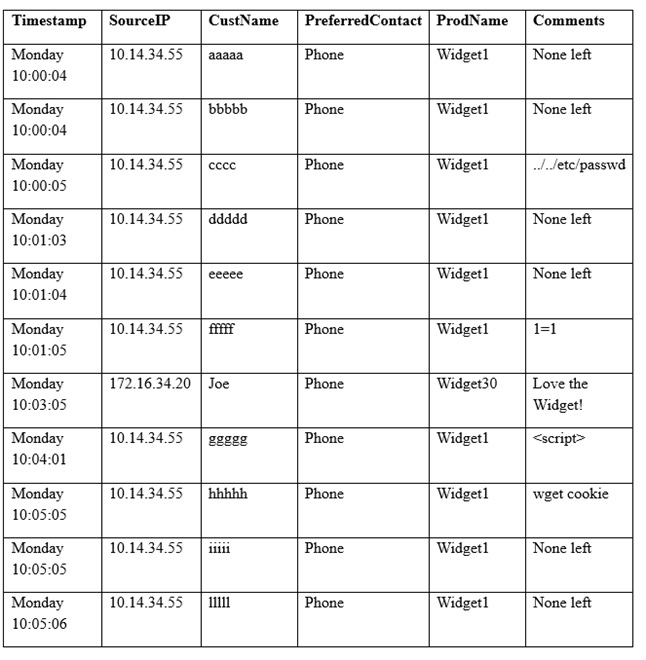
Which of the following is the MOST likely type of activity occurring?
A. SQL injection
B. XSS scanning
C. Fuzzing
D. Brute forcing
Correct Answer: A
