While reviewing web server logs, a security analyst notices the following code:
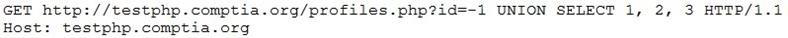
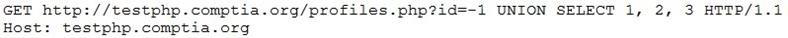
Which of the following would prevent this code from performing malicious actions?
A. Performing web application penetration testing
B. Requiring the application to use input validation
C. Disabling the use of HTTP and requiring the use of HTTPS
D. Installing a network firewall in front of the application

wrong answer
B:Requiring the application to use input validation
SQL injection
Good catch. Thanks